How Malicious Software Impacts Law Firms
The American Bar Association completed a TECHREPORT in 2017 to investigate the impact of cyber security breaches on law firms.
According to the American Bar Association: “The 2017 Survey responses make it difficult to tell how many breaches there have actually been with exposure of client data because almost 5% overall report that they don’t know about the consequences. This includes ‘don’t know’ responses by 3% in firms of 10-49 [attorneys], 8% of firms of 50-99, 25% of firms of 100-499, and 14% of firms of 500+. The uncertainty is increased by the high percentage of respondents (22%), discussed above, who don’t even know whether their firm experienced a data breach.”
According to research from the Verizon RISK Team, few breaches are unique, meaning the vast majority of incidents are caused by a small number of scenarios. Verizon classifies 18 different data breach scenarios into four groups; the human element, conduit devices, configuration exploitation and malicious software. For the purposes of this article, we will focus on the malicious software that makes institutions vulnerable.
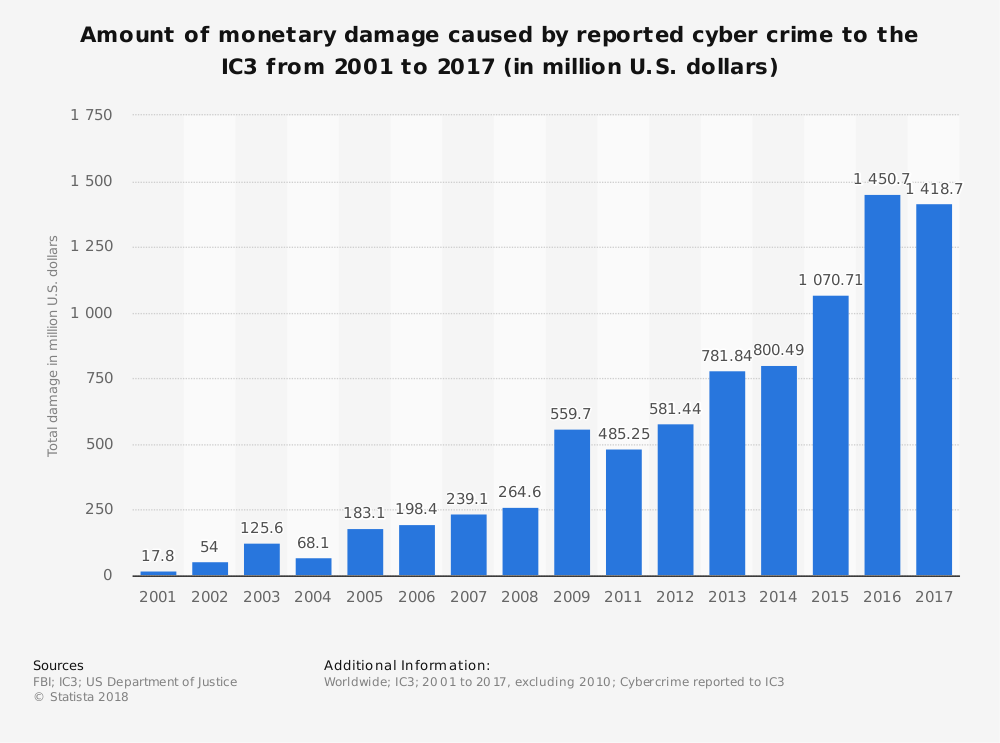
Verizon’s 2018 Data Breach Investigation Report states that over 75% of confirmed data breaches were financially motivated.
 They go on to report that ransomware is at the top variety of malicious software, being found in 39% of cases.
They go on to report that ransomware is at the top variety of malicious software, being found in 39% of cases.
The lesson here is that malware is a big contributor to the breach landscape and it is rare that malware acts alone.
These malicious software attacks can generally be defined as one of the four categories listed below.
Table of Contents
1. Ransomware
Ransomware is a form of malware that uses encryption to lockout institutions from accessing their files. The attacker basically holds the data hostage until the user agrees to pay a ransom to regain access to their data. This type of attack increased by 36 percent in 2017, introducing 100 new malware types.
Ransomware is on the rise and law firms are especially vulnerable. One common type of ransomware is CryptoLocker, a Trojan that targets computers that run Microsoft Windows. The malware encrypts data with an accompanying message that the data will be decrypted once a ransom of Bitcoins is paid by a set deadline.
So what does the FBI recommend? “As ransomware techniques and malware continue to evolve—and because it’s difficult to detect a ransomware compromise before it’s too late—organizations [that house personal data] in particular should focus on two main areas:
- Prevention efforts—both in terms of awareness training for employees and robust technical prevention controls; and
- The creation of a solid business continuity plan in the event of a ransomware attack.”
2. Sophisticated Malware
Sophisticated malware attacks include custom-written viruses designed to disable a system’s security and its anti-virus measures. As suggested in its name, the attacks are highly advanced and often targeted towards specific institutions with well-established IT security implementations in place. While breach detection time dropped significantly to 146 days in 2015 from 416 days in 2012, some malware can still go undiscovered for years.
According to the FBI:
“Ransomware attacks are not only proliferating, they’re becoming more sophisticated. Several years ago, ransomware was normally delivered through spam e-mails, but because e-mail systems got better at filtering out spam, cyber criminals turned to spear phishing e-mails targeting specific individuals.
And in newly identified instances of ransomware, some cyber criminals aren’t using e-mails at all. According to FBI Cyber Division Assistant Director James Trainor, ‘These criminals have evolved over time and now bypass the need for an individual to click on a link. They do this by seeding legitimate websites with malicious code, taking advantage of unpatched software on end-user computers.’”
{{cta(‘148f4bfd-14e1-4e10-bd9a-11e5c59b0a43’)}}
3. RAM Scraping
Certain malware, known as RAM scraping, is designed to extract data from physical memory and typically targets point-of-sale (POS) systems. This malware targets the POS terminal during the brief vulnerable period when a transaction is taking place.
The now-infamous Target breach in 2013 is a prime example of hackers utilizing RAM scraping to steal the card information of more than 110 million Target customers. The attack went on for nearly two weeks before it was detected.
4. Credential Theft
When credentials are stolen, it is difficult to detect a malicious “known user.” Using spyware/keylogger, stolen credentials, phishing, backdoor and password dumber tactics, these attacks allow threat actors to pose as a known user and gain carte blanche access to the network for months (if not longer), placing a great amount of data at risk. To prevent credential theft, Verizon recommends a strong password policy, two-factor authentication, patching vulnerabilities immediately, reviewing network logs and addressing the SQL injection issues.
Malware Protection from Your MSP
Eternal vigilance, quick identification and the right protections are key to avoiding major damage from a malicious software attack. Fairdinkum employs a combination of cutting-edge techniques to ensure your infrastructure is safe, up-to-date, scalable and compliant, keeping your company in good standing.